Why verifying suspicious messages protects you (98% open)
TL;DR:
- Text messages have a 98% open rate, making them a prime target for scammers.
- Scams rely on social engineering and urgency to manipulate even cautious individuals.
- Verifying messages through official sources and using simple habits can prevent financial and identity loss.
Text messages are opened at a 98% open rate), which means scammers have an almost guaranteed audience every time they send a fake alert. And here’s the uncomfortable truth: it’s not just careless or uninformed people who fall for these traps. Smart, cautious adults get caught too, because scammers have become very good at using psychology against us. Whether you’re a parent keeping your kids safe online or a small business owner protecting your finances, verifying suspicious messages is one of the most powerful habits you can build. This guide walks you through exactly why it matters and how to do it.
Table of Contents
- How scams exploit trust in everyday messages
- The real risks of acting on unverified messages
- How to verify a suspicious message: Step-by-step
- Protecting families and small businesses: Special considerations
- Why instant verification is your secret weapon against scams
- Stay safer with proven verification tools
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Verification blocks scams | Pausing to verify suspicious messages stops scams before they cause harm. |
| Financial losses are rising | Text scam losses hit $470 million in 2024, showing increasing risk for individuals and businesses. |
| Use official channels | Always verify unexpected messages by contacting an organization directly through their official website. |
| Protect vulnerable users | Families and small businesses should teach everyone to verify, not just tech-savvy individuals. |
How scams exploit trust in everyday messages
With the risks clear, let’s explore how scammers are so successful at manipulating even cautious people.
Scammers don’t rely on technical wizardry. They rely on trust. Most of us have been trained to respond quickly to texts from our bank, a delivery company, or a family member. Scammers know this and use it against us every single day.
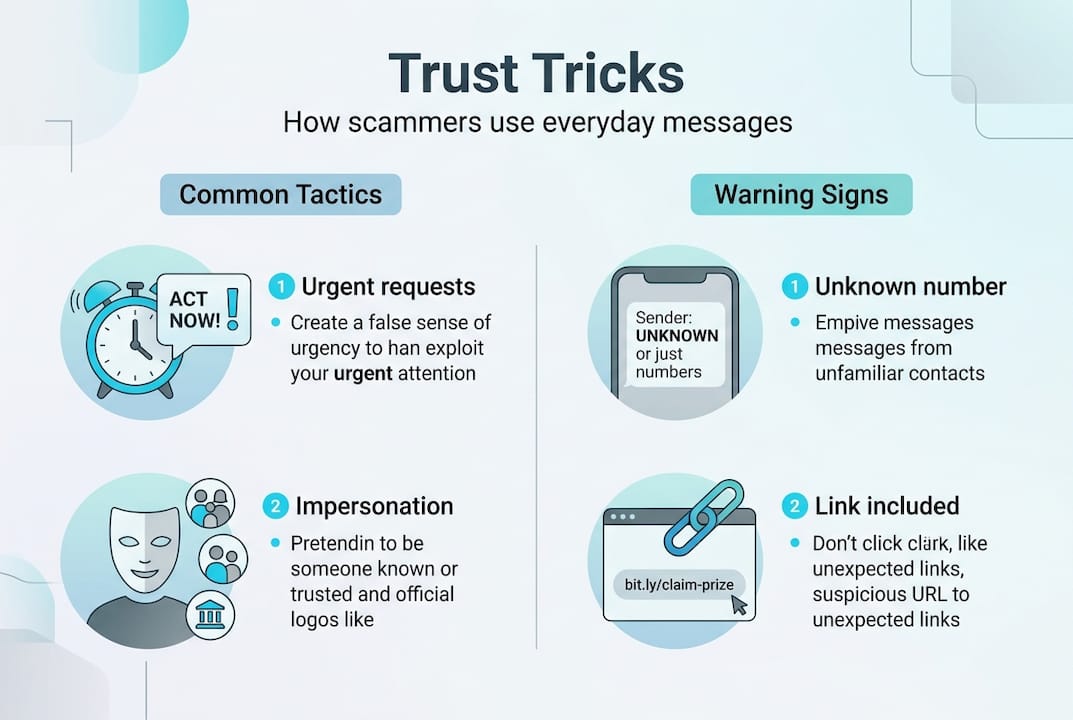
This tactic is called social engineering: using emotion and psychology rather than hacking to trick someone into acting fast. The message doesn’t need to look perfect. It just needs to feel urgent enough that you don’t stop to think.
Here are some of the most common message types scammers use:
- A text claiming your bank account has been locked and you need to verify your identity immediately
- A delivery notification saying your package is held and you owe a small customs fee
- A message pretending to be from a family member saying they lost their phone and need money fast
- A fake government alert saying you owe taxes and face arrest unless you pay now
Each one is designed to create panic. Panic short-circuits your judgment.
“Smishing (SMS phishing) exploits the fact that texts carry a sense of immediacy and personal trust that email simply doesn’t match. That’s exactly why 98% open rates) make it such a dangerous scam vector.”
The financial damage is staggering. Consumers lost $470 million to text scams in 2024 alone. That’s not a small group of careless people. That’s millions of ordinary Americans who got a message at the wrong moment and clicked before they thought it through.
Learn to recognize the SMS scam warning signs before they catch you off guard. If you want a practical breakdown, see how to identify text scams with specific real-world examples.
The real risks of acting on unverified messages
Understanding the methods isn’t enough. It’s crucial to see what can actually go wrong if you skip verification.
Interacting with malicious links) can lead to financial loss, identity theft, or a compromised device. And the risk escalates with each step you take inside a scam.
Here’s how the danger builds:
- You open a suspicious message. No immediate harm yet, but your guard is down.
- You click a link. The site may silently install malware or record your device info.
- You enter personal details. Name, address, and date of birth can be sold or used to open accounts in your name.
- You share financial info. Bank account or card numbers go directly to criminals.
- You send money. Once a wire transfer or gift card payment is made, recovery is nearly impossible.
The consequences fall into three main categories:
| Risk type | What it means for you | Recovery difficulty |
|---|---|---|
| Financial loss | Direct theft of funds or purchases | High, often irreversible |
| Identity theft | Fraudulent accounts opened in your name | Very high, takes months |
| Device compromise | Malware installed, data stolen silently | Moderate to high |
In 2024, text scam losses reached $470 million across the U.S. That figure doesn’t include the hours of stress, legal paperwork, and credit monitoring that victims face afterward.
Replying to a scam message also confirms your number is active, making you a target for more attacks. Even a simple “Stop” reply can backfire. The safest move is always to verify first through an official source, never through the message itself.

For a broader picture of how these threats connect, read about phishing email threats and explore scam avoidance strategies that work across all channels. It also helps to look at real scam message examples so you know exactly what to watch for.
How to verify a suspicious message: Step-by-step
Knowing the stakes, you need a repeatable process to stay safe every time.
The good news is that verification doesn’t have to be complicated. Once it becomes a habit, it takes less than two minutes and protects you from the vast majority of attacks.
Here’s a step-by-step process you can follow:
- Pause. Don’t click, reply, or call any number listed in the message. Take a breath.
- Check the sender. Look at the phone number or email. Official organizations rarely use random numbers or free email domains.
- Go directly to the source. If the message claims to be from your bank, type your bank’s web address directly into your browser. Don’t use the link in the message.
- Look up the official number. Call the company using the number on their real website, not the one in the text.
- Scan any suspicious link safely. Use a URL risk checker to preview the destination before you ever click.
- Report it. Forward the message to 7726 (the carrier spam reporting shortcode), file a report with the FTC at reportfraud.ftc.gov, or block the number.
The FTC recommends not clicking, verifying through official channels, and reporting suspicious messages as the three core steps every person should take.
Here’s a quick comparison of safe versus risky responses:
| Action | Safe | Risky |
|---|---|---|
| Click the link in the message | ✗ | |
| Go to the official website directly | ✓ | |
| Reply to confirm your number | ✗ | |
| Use a URL checker to scan the link | ✓ | |
| Call the number listed in the text | ✗ | |
| Report to 7726 or FTC | ✓ |
Pro Tip: If you get a suspicious package delivery text, use the USPS scam text check tool before doing anything else. Fake delivery scams are one of the most common types right now.
For a broader look at how scams are structured, our guide on scam spotting techniques covers everything from fake invoices to impersonation attacks.
Protecting families and small businesses: Special considerations
General steps work, but families and businesses face unique risks and have real opportunities to build a verification culture.
Children and seniors are prime targets for scammers. Kids may not recognize social engineering, and older adults are often targeted with Medicare, Social Security, or grandparent scams. Staff at small businesses are targeted too, especially through fake invoice texts or messages pretending to be from the boss.
Building a safety culture means making verification a shared habit, not just a personal one.
Here’s how to make it stick for families and small teams:
- Teach the “pause, verify, report” rule. Make it a family or team mantra. Before anyone acts on a message, they pause, verify through an official source, and report if it’s suspicious.
- Set up a household or team channel for suspicious messages. When someone gets a weird text, they share it with the group before doing anything.
- Never rely on SMS alone for account security. SMS-based authentication can be intercepted. Use an authenticator app for important accounts instead.
- Practice with real examples. Sit down with kids or staff and show them what actual scam messages look like so they can recognize the patterns.
- Make it normal to ask. No one should feel embarrassed about saying, “Can you check if this is real?” Shame keeps people quiet about scams they almost fell for.
Pro Tip: You can set up ScamKit for families to give parents and seniors a simple, private way to check suspicious messages without needing any technical knowledge. No account needed.
For small businesses, the risk extends beyond personal finances. A single employee clicking an unverified link can expose customer data, trigger a breach notification, or result in wire fraud. Training your team on verification is not optional. It’s a basic operational protection.
Why instant verification is your secret weapon against scams
Let’s reconsider what truly shields us from scammers, beyond strong passwords and security apps.
Most people focus on the wrong thing. They install antivirus software, set complex passwords, and enable two-factor authentication. All of that is useful. But none of it stops you from handing your credentials directly to a scammer because an urgent text made your heart race.
The real breakthrough is behavioral. It’s the pause.
Every scam depends on urgency. The moment you slow down and verify, the scammer loses. No legitimate organization) will ever demand that you take immediate action through an unsolicited message. That urgency is the scam. Recognizing it is the defense.
This is why we believe instant verification is more powerful than any app or filter. Tools help, but the person holding the phone is always the first and most important line of defense. When you train yourself and the people around you to pause before reacting, you break the entire model that scammers rely on.
Building safe messaging habits doesn’t require technical skill. It requires a simple shift: treat every unsolicited message as unverified until proven otherwise.
That one mental habit defeats social engineering before it even gets started.
Stay safer with proven verification tools
If you’re ready to put message verification into practice, these resources make it easy for anyone to get started.
ScamKit was built specifically for moments like this. When a suspicious message shows up and you’re not sure what to do, you need answers fast and without complicated steps.
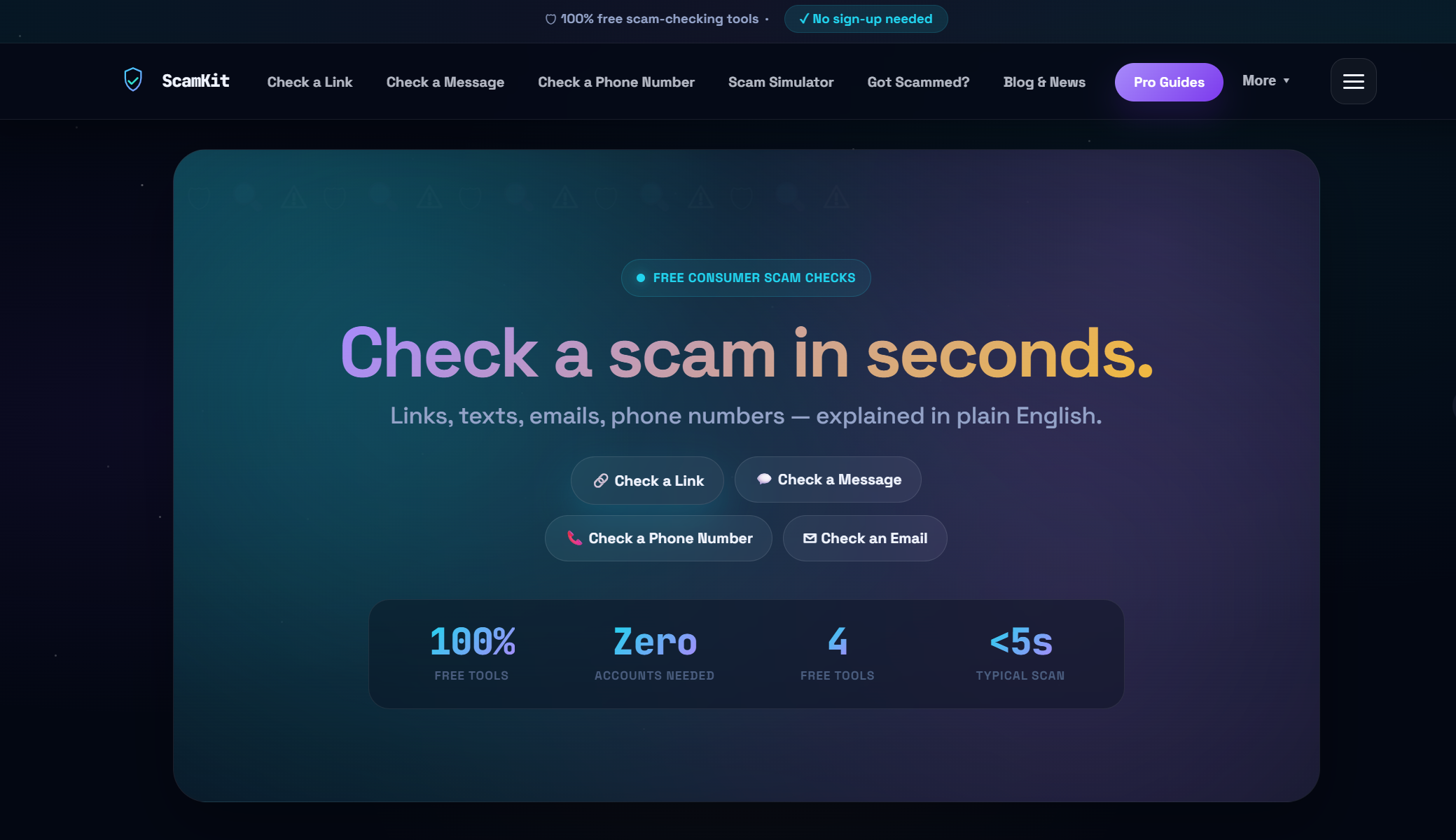
With ScamKit’s free link checking tools, you can scan any URL before you click it, with no account required. Want to train your family or staff? The scam detection simulator walks users through realistic scenarios so they know exactly what to look for. And if you want to understand the bigger picture, explore the proactive cybersecurity approach that helps households and small businesses stay ahead of threats before they arrive.
Frequently asked questions
What is the most important step if I receive a suspicious message?
Never click links or reply to the message. Go directly to the sender’s official website or call their published number to verify whether the message is real.
How do scammers make their messages seem legitimate?
Scammers impersonate trusted organizations) and use urgent, threatening language designed to create panic and push you into acting before you think it through.
Why is verifying messages important for children or the elderly?
Children and seniors are frequent scam targets because they may not recognize manipulation tactics, making it especially important for families to teach the pause, verify, and report habit early.
Are business owners targeted by message scams too?
Yes. Falling for scams) can expose business systems to fraud, data breaches, or direct financial theft, making verification a critical practice for any organization, no matter its size.