How to spot scams: step-by-step guide to stay safe online
TL;DR:
- Modern scams use AI and emotional manipulation to appear highly convincing and real.
- Building verification habits and using tools like URL checkers can help detect scams early.
- Slowing down, verifying independently, and discussing suspicious messages protect against increasingly sophisticated frauds.
Last year, a friend of mine nearly wired $3,000 to someone pretending to be her bank’s fraud department. The caller knew her name, her account balance, and even the last four digits of her card. She almost did it. The only thing that stopped her was a habit she had built months earlier: always hang up and call back using the number on the back of your card. That habit saved her. In 2024, U.S. consumers lost $12.5 billion to fraud, and the numbers keep climbing. Scammers are not getting lucky. They are getting smarter. This guide gives you the exact steps to recognize, avoid, and respond to online scams before they cost you.
Table of Contents
- Understand the latest scam tactics
- Gather your scam-spotting tools and habits
- Step-by-step: Verify, check, and respond safely
- Tailored defenses for families and small businesses
- Why relying on intuition alone is not enough
- Quick tools to help you spot scams faster
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Recognize red flags | Scams use urgency, secrecy, and untraceable payments—look for these warning signs. |
| Always verify independently | Check any request for money or info with official sources, not the contact provided. |
| Use digital tools | Link checkers, email analyzers, and security habits help catch sophisticated scams early. |
| Protect families and businesses | Teach family code words and train employees regularly for layered defense. |
| Don’t trust your gut | Modern scams defeat intuition; use a checklist and verification process every time. |
Understand the latest scam tactics
Scammers are not the clumsy, obvious fraudsters they used to be. Today, they use psychology, technology, and detailed personal data to make their attacks feel completely real. Understanding their methods is your first line of defense.
Imposter scams are the most common threat. Fraudsters pose as the IRS, Social Security Administration, Amazon, your bank, or even a family member in trouble. According to the FTC, imposter scam details show this category consistently tops fraud reports year after year. The caller or sender sounds legitimate because they do their homework first.
What makes modern scams especially dangerous is AI. AI-enhanced scams like deepfakes and voice cloning now make impersonation harder to detect than ever. A scammer can clone your adult child’s voice using just a few seconds of audio pulled from social media, then call you claiming they are in danger and need money immediately. That is not science fiction. It is happening right now.
Here is a comparison of old-school versus modern scam tactics:
| Old-school scams | Modern AI-powered scams |
|---|---|
| Generic email blasts | Personalized, targeted phishing |
| Obvious fake caller IDs | Spoofed numbers matching real businesses |
| Poor grammar and spelling | Polished, professional language |
| Static fake websites | Dynamic sites with real SSL certificates |
| Text-only impersonation | Voice cloning and deepfake video |
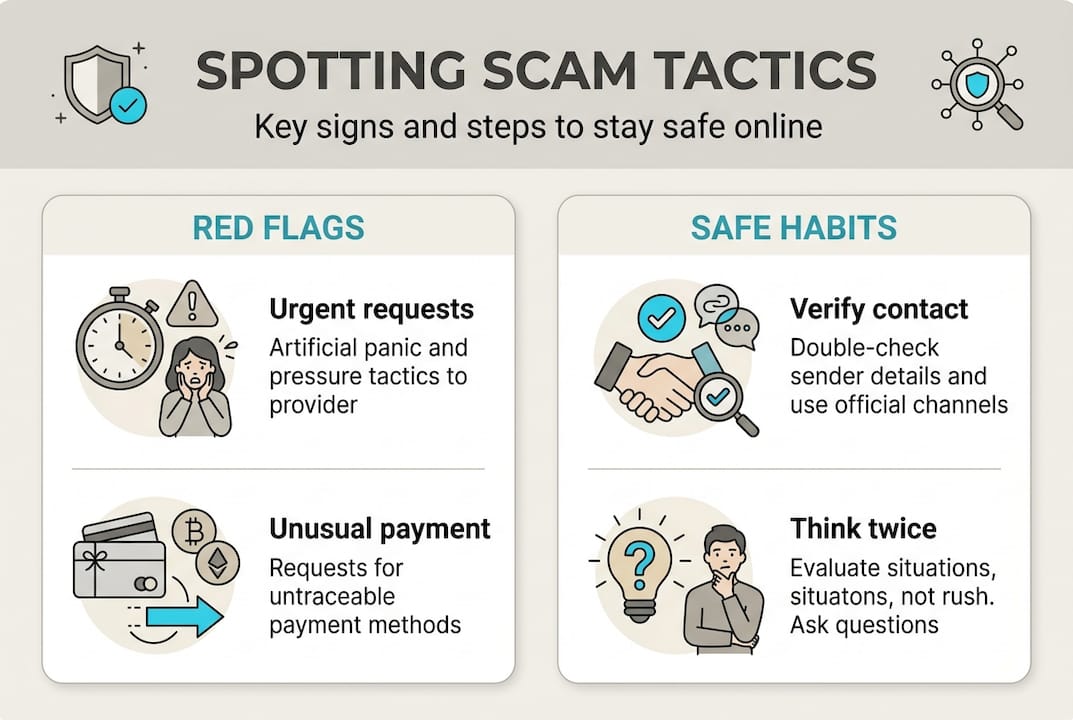
Regardless of the method, scammers rely on a core set of pressure tactics. The signs of a scam you should watch for include:
- Urgency: “Act now or your account will be closed.”
- Secrecy: “Don’t tell anyone about this.”
- Untraceable payment requests: gift cards, wire transfers, or cryptocurrency
- Fake caller ID or spoofed email addresses
- Requests for personal information out of the blue
“If someone pressures you to act fast and keep it secret, those are two of the biggest red flags there are. Slow down. Real organizations do not operate that way.”
Your gut can sometimes tell you something feels off, but modern scams are engineered to override that feeling. Scammers use emotion, authority, and familiarity to short-circuit your instincts. That is why you need more than a feeling. You need a system. Exploring solid scam avoidance strategies is a great starting point for building that system.
Pay special attention to voice cloning scams and learn how to spot deepfake scams before you encounter one in real life. The more familiar you are with these tactics, the harder you are to fool.
Gather your scam-spotting tools and habits
Recognizing the tactics is the first step. Now, set up simple routines and tools to stay a step ahead of scammers every day.
You do not need to be a tech expert to protect yourself. You just need the right habits and a few reliable tools in your corner.
Build your personal verification checklist. Before you click a link, send money, or share information, run through these steps:
- Did this contact come out of nowhere?
- Is there pressure to act immediately?
- Are they asking for an untraceable payment method?
- Can I verify this request through an independent source?
- Does the sender’s address or phone number match official records?
When it comes to digital tools, a URL checker is one of the most practical things you can use. Search result scams exploit fake ads and misleading links, so always verify sites directly or through organic search results rather than clicking paid ads. Email header analyzers can reveal whether an email actually came from the domain it claims to be from. Anti-phishing browser extensions add another layer of screening.

Here is a quick reference table for tools and their best uses:
| Tool type | What it catches | Best for |
|---|---|---|
| URL checker | Fake or malicious websites | Before clicking any link |
| Email header analyzer | Spoofed sender addresses | Suspicious emails |
| Phone number screener | Known scam numbers | Unexpected calls |
| Anti-phishing software | Phishing pages in real time | Daily browsing |
While phishing detection models can reach up to 99% accuracy in lab benchmarks, real-world scams are designed to slip past automated filters. That means you cannot rely on software alone. Your habits matter just as much.
Pro Tip: Never use the contact information provided in a suspicious message to verify it. Always look up the official number or website independently. This single habit catches a huge percentage of scam attempts.
For a deeper walkthrough, check out these online scam prevention steps and learn how to check phone scams before you pick up or call back.
Healthy skepticism toward unsolicited offers is not paranoia. It is just smart. If an ad, email, or call seems too good or too urgent, treat it as suspicious until proven otherwise. Checking recognizing scam signs regularly keeps your radar sharp.
Step-by-step: Verify, check, and respond safely
Preparation is great, but the moment you suspect a scam is when it counts. Here is how to act calmly and effectively.
When something feels off, your first move should always be to pause. Do not click. Do not pay. Do not reply. This three-step pause saves more people than any software tool.
Here is your action plan for suspicious contacts:
- Stop immediately. Close the message or hang up the call without engaging further.
- Write down the details. Note the number, email address, or URL while it is fresh.
- Verify independently. Look up the organization’s real contact information from their official website, then reach out through that channel only.
- Check the request. Real banks, government agencies, and businesses will never ask for gift cards or wire transfers to resolve an issue.
- Report it. File a report at ReportFraud.ftc.gov and notify your bank if financial information was involved.
- Talk to someone. Before taking any action, run the situation by a trusted friend, family member, or colleague.
For suspicious emails specifically, phishing email analysis can help you break down what you are actually looking at. Understanding the anatomy of a fake email makes it much easier to identify in the future.
“Slow down, talk to someone you trust, and verify contacts independently using info you already know is real. Never use the number or link they give you.”
The FTC also notes that pressure and secrecy are key scammer tactics. If someone is rushing you or asking you to keep things quiet, those are signals to slow down, not speed up.
Pro Tip: Create a family code phrase for emergency calls. If someone calls claiming to be your child in trouble, ask them for the code word. Scammers using voice cloning will not know it.
For a broader look at tactics and countermeasures, the guide on how to spot and avoid scams walks through the most common scenarios with practical responses.
If you suspect you have already been targeted, contact verifying imposter claims to understand your next steps and protect your accounts.
Tailored defenses for families and small businesses
Individuals are not alone in being targeted. Families and small businesses face unique threats. Here is how to build extra layers of defense.
For families, communication is your strongest tool. Agree on a code word that only your immediate family knows. Use it to verify anyone claiming to be a family member in an emergency. This is especially important because older adults lost over $5 billion in 2024, often through AI voice cloning used in fake emergency frauds.
Key steps for families:
- Talk openly with children and older relatives about what scams look like
- Explain that real emergencies do not require secrecy or untraceable payments
- Practice the “hang up and call back” rule for any unexpected urgent calls
- Use AI voice cloning scams resources to show older family members real examples
- Set a rule: nobody sends money without talking to at least one other family member first
Pro Tip: Sit down with elderly relatives and walk through a fake scam call together. Roleplay builds recognition faster than any warning ever could.
For small businesses, the stakes are equally high. Social engineering is the top threat small businesses face, and it is best mitigated through employee training, multi-factor authentication (MFA), and strong network protections.
Here is a quick defense framework for small business owners:
| Defense layer | Action to take | Priority |
|---|---|---|
| Staff training | Regular scam awareness sessions | High |
| Multi-factor authentication | Enable on all business accounts | High |
| Network protection | Firewall, VPN, and endpoint security | Medium |
| Incident response plan | Document steps if a breach occurs | Medium |
| Vendor verification | Confirm payment changes by phone | High |
NIST recommends risk management frameworks, MFA, asset identification, anomaly detection, and documented incident response plans for small businesses. If you do not have internal IT capacity, consider bringing in outside help even for a basic security review.
Familiarizing your team with understanding scam templates is one of the most cost-effective training moves you can make. Also, review business impersonation tips from the FTC to understand how scammers specifically target small business owners.
Why relying on intuition alone is not enough
Even with all these defenses in place, it is tempting to trust your gut. But here is the honest truth: in 2026, that is not enough.
Human intuition worked reasonably well against older scams because those scams had obvious flaws. Bad grammar. Generic scripts. Implausible stories. But AI-powered scams are designed by algorithms trained on millions of successful deceptions. They are optimized to feel real.
Imagine getting a call that sounds exactly like your sister, crying, saying she was in a car accident and needs bail money right now. Your gut floods with fear and love. That is exactly what the scammer is counting on. No checklist feels natural in that moment. But a checklist is precisely what saves you.
Relying on gut instinct is measurably less effective against AI-driven scams. Processes and independent verification are stronger defenses. The people who avoid scams in 2026 are not the ones with the best instincts. They are the ones who built the right habits and follow them even when emotions run high.
Build those habits now, not after a close call. Review your avoidance best practices regularly and treat verification as a routine, not an insult to the person contacting you.
Quick tools to help you spot scams faster
Knowledge is powerful, but having the right tools makes it automatic. ScamKit was built specifically so that anyone, with no technical background, can check whether a link, email, or message is suspicious in seconds.
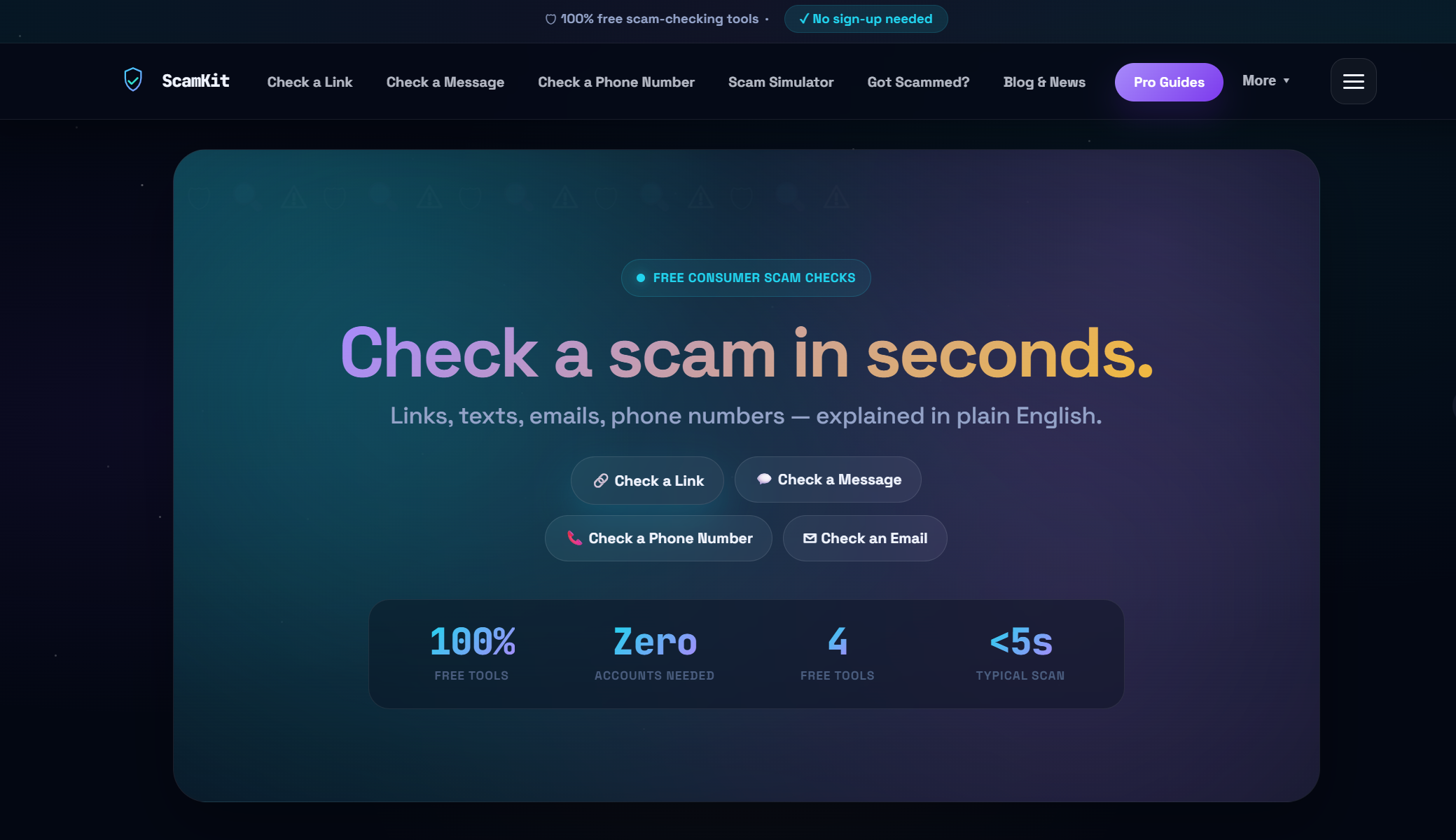
You can check suspicious links instantly without signing up or sharing your personal data. If a strange email lands in your inbox, use ScamKit to analyze suspicious emails and get a fast risk breakdown. For families and small businesses ready to take things further, the proactive cybersecurity resources on ScamKit walk you through building stronger long-term defenses. No jargon, no complicated setup. Just fast, reliable protection that respects your privacy.
Frequently asked questions
What are the top signs of an online scam?
Pressure to act fast, requests for secrecy, demands for gift cards or crypto, and unexpected contacts from strangers or impersonators are the biggest warning signs. The FTC confirms that urgency and untraceable payments are consistent red flags across nearly every scam type.
How can I confirm if a call or email is real?
Always look up the official contact information yourself and reach out through that channel. The FTC advises you to verify contacts independently using info you already know is legitimate, never through links or numbers provided in the suspicious message.
What should I do if I suspect a scam message or call?
Do not respond, click, or pay anything. The FTC recommends you talk to someone trusted before acting, then report the incident to the FTC at ReportFraud.ftc.gov or notify your bank directly.
How are scammers using AI to trick people?
Scammers now use deepfakes and voice cloning to create convincing fake identities, mimic the voices of loved ones, and generate emergency scenarios designed to trigger panic. AI-enhanced scams make traditional detection much harder, which is why systematic checks matter more than ever.
What extra steps should small businesses take to avoid scams?
Prioritize regular employee training on social engineering, enforce phishing-resistant MFA on all accounts, and keep network security tools updated. Experts at cybersecurity for small business consistently point to these three measures as the highest-impact defenses available to small organizations.