How to recognize and stop impersonation scams

TL;DR:
- Impersonation scams pretend to be trusted entities to manipulate victims into sending money or personal info.
- Scammers use spoofed calls, emails, and AI voice cloning to appear convincing and urgent.
- Building automatic verification habits and reporting scams can help prevent victimization.
I first came across a story about impersonation scams when a coworker’s mother, a retired teacher who was careful with her finances, nearly wired $9,000 to someone claiming to be a Social Security official. She wasn’t naive. She wasn’t careless. She was scared, and that fear made all the difference. Impersonation scams are now one of the fastest-growing forms of online fraud, with Americans losing $2.95 billion to imposter scams in 2024 alone. This guide will walk you through exactly what these scams are, how they work, who they target, and what you can do right now to protect yourself and your family.
Table of Contents
- What is an impersonation scam?
- How impersonation scams work: Tactics and technology
- Common types of impersonation scams and who they target
- How to spot, stop, and report impersonation scams
- The uncomfortable truth about impersonation scams: Why education still falls short
- How ScamKit can help you stay protected
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Impersonation scams defined | Scammers pose as trusted people or entities to trick you into sending money or information. |
| Top scam tactics | Authority, urgency, spoofed channels, and emotional manipulation are hallmarks of these scams. |
| Vulnerable targets | Older adults and anyone unfamiliar with scam signs are at highest risk. |
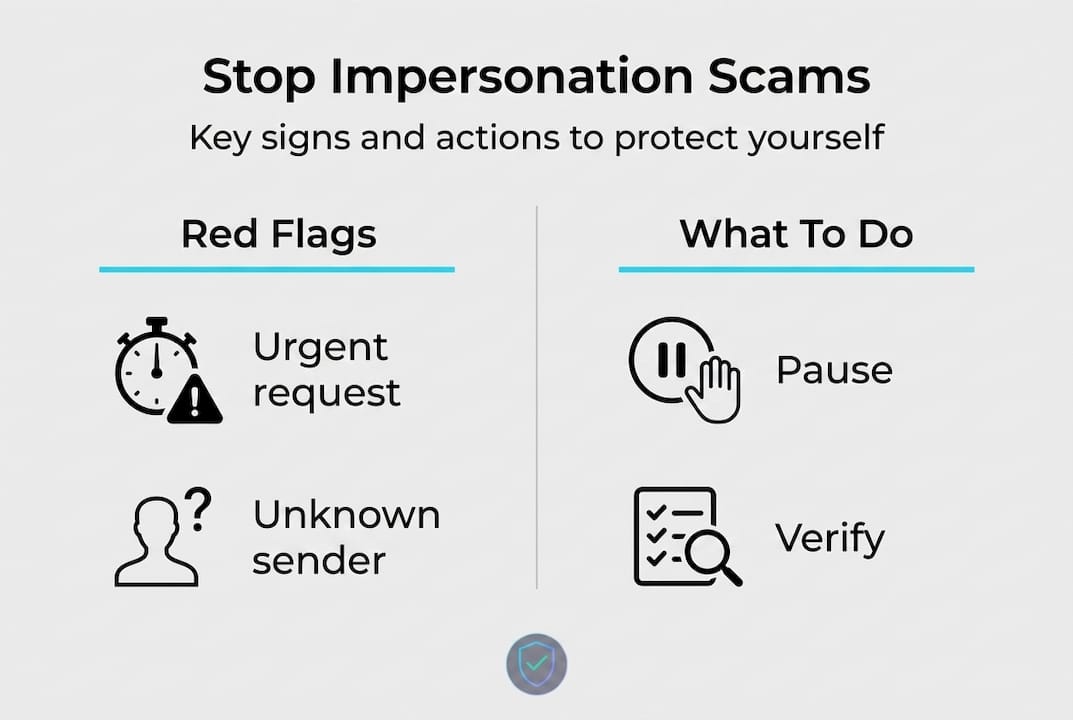
| Practical defenses | Pause, verify with official sources, and never trust contact details in suspect messages. |
| Report and prevent | Reporting scams and spreading awareness help reduce risks for everyone. |
What is an impersonation scam?
Now that you see the staggering impact, let’s define what these scams really are and why they’re so convincing.
An impersonation scam, also known as an imposter scam, occurs when a scammer pretends to be a trusted entity, whether that’s a government agency, your bank, a tech company, or even a family member. The scammer’s identity is fake. The pressure they create is very real.
These scams happen across almost every communication channel you use. That includes:
- Phone calls: Fake IRS agents, Medicare representatives, or Social Security officials
- Text messages: Spoofed bank alerts warning of unauthorized charges
- Emails: Convincing messages that mimic your email provider or credit card company
- Social media: Cloned profiles from people you know, asking for money or a favor
The end goal is always the same. Scammers want to manipulate you into one of three outcomes: sending them money, handing over personal information like your Social Security number or passwords, or giving them remote access to your computer or accounts.
Understanding phishing email tactics is a critical part of staying safe, since many impersonation scams begin with a well-crafted fake email. The same applies to social media scam warning signs, where cloned or fake profiles create a false sense of familiarity.
“The scammer always plays someone you’d trust without thinking. That’s what makes impersonation scams so dangerous. You don’t stop to question a call from your bank or a text from your Medicare provider.”
The hardest part to accept is that no communication channel is completely safe. If you receive a message that asks you to act immediately, that alone should raise a red flag.
How impersonation scams work: Tactics and technology
With a clear definition in mind, let’s dig into how these scams are actually perpetrated and why they’re so effective.
The core mechanics are surprisingly consistent across every type of impersonation scam. Scammers spoof caller ID, use fake websites, and create urgency or threats to trick victims. The technology has changed. The playbook hasn’t.
Here’s how a typical scam unfolds:
- Contact is made: You receive a call, text, or email from what appears to be a known and trusted source. The phone number might look like your bank’s official line. The email might be nearly identical to one you’ve received before.
- Authority is established: The scammer introduces a believable identity. “This is Officer Collins from the Social Security Administration.” Or, “I’m calling from your bank’s fraud prevention team.”
- Urgency is injected: You’re told something has gone wrong. Your account is compromised. You owe back taxes. A family member is in trouble. You need to act right now.
- Pressure escalates: The scammer warns you not to hang up, not to tell anyone, and not to verify with anyone else. This isolation is deliberate and calculated.
- The ask arrives: You’re told to buy gift cards and read out the numbers, transfer money via wire, pay with cryptocurrency, or share a one-time passcode.
Modern scammers have added frightening new tools to this playbook. AI voice cloning risks are now a real threat, allowing criminals to replicate a family member’s voice with just a few seconds of audio pulled from social media. There are documented cases where grandparents received calls that sounded exactly like their grandchildren crying for help. When you’re hearing what sounds like your grandson’s voice saying “Grandma, I’m in jail, please don’t tell Mom,” the emotional response can override all rational thinking.
Government official impersonation complaints doubled in 2025, a rise that the FBI links partly to AI tools but also to core tactics that have stayed exactly the same for decades. It’s a reminder that technology amplifies the scam, but psychology drives it.
For detecting fake emails and spotting AI deepfakes, there are reliable techniques. Look for mismatched sender addresses, strange formatting, and any message that pushes you to act before you think.
Pro Tip: If anyone contacts you and insists you keep the call secret from family members or tells you not to hang up and verify, treat it as a scam. Legitimate institutions never ask for secrecy.
Common types of impersonation scams and who they target
Having unpacked the tactics, let’s see where these scams show up, which types are most common, and who’s most at risk.
Impersonation scams are not one-size-fits-all. They’re tailored, specific, and designed to exploit the exact fears or situations their targets face. The most common categories include government, bank and business, tech support, grandparent or family emergency, charity, and unemployment scams.
Here’s a breakdown of the most prevalent types:
| Scam type | How contact is made | The fake identity | The ask |
|---|---|---|---|
| Government impersonation | Phone call or email | IRS, SSA, Medicare, FTC | Pay back taxes, owed fines, or arrest warrants |
| Bank and business | Text or call | Your bank, PayPal, Amazon | Confirm your identity, reverse fraud |
| Tech support | Pop-up alert or email | Microsoft, Apple, Google | Allow remote access to your device |
| Grandparent or family | Phone call | A grandchild, attorney, or police | Emergency bail money or hospital fees |
| Charity | Email or social media | Known nonprofits | Donate via wire or gift card |
| Unemployment | Email or website | State labor departments | Verify your identity to receive benefits |
Bank impersonation scams often begin with a text message that looks exactly like the real fraud alerts your bank sends. You’re told unusual activity has been detected. You click a link, land on a convincing fake website, and enter your login credentials. By the time you realize something is wrong, the damage is done.

Older adults are disproportionately affected. The FTC reports a four-fold increase in reports of losses of $10,000 or more from people 60 and older since 2020. That’s not because older adults are less intelligent. It’s because they often have more savings, are more trusting of authority figures, and may be less familiar with the patterns these scams follow.
Key groups that scammers target most aggressively:
- Adults aged 60 and older, especially for government and tech support scams
- People going through financial stress, since they’re more likely to respond to offers of help
- Small business owners, who receive fake vendor or bank fraud alerts
- Immigrants, who may fear government contact and respond to threats of deportation or legal action
- Parents and grandparents, who will act fast when they believe a loved one is in danger
Understanding scam avoidance strategies and sharing phone scam verification tips with older family members can make a real difference. These scams are preventable when the right information is available.
How to spot, stop, and report impersonation scams
Once you know who’s targeted and how, it’s essential to master the tools for personal protection. Here’s how to recognize, halt, and report these scams in practice.
Scams rely on social engineering over technical exploits, meaning the goal is to manipulate your emotions, not hack your device. Social engineering is the practice of psychologically manipulating people into revealing information or taking actions they normally wouldn’t. Slowing down is your most powerful defense.
Follow these steps if you suspect a scam:
- Pause immediately. Before you respond, send money, or share anything, stop. Take a breath. Scammers need you to act now. You don’t have to.
- Do not use the contact information provided. Hang up. Close the chat. Delete the text temporarily. Do not call back using the number that called you.
- Verify independently. Look up the official number on the institution’s real website. Call that number directly. Ask whether the contact was real.
- Do not share one-time codes. Banks and real service providers will never ask you to read a security code over the phone.
- Never pay with gift cards, wire transfers, or cryptocurrency. These payment methods are untraceable and irreversible. Real institutions do not use them.
- Report the scam. File a report at reportfraud.ftc.gov, contact your bank immediately, and tell someone you trust.
Here’s a quick reference for reporting:
| Where to report | What they handle |
|---|---|
| FTC at reportfraud.ftc.gov | General scam reports |
| Your bank or credit card issuer | Unauthorized transactions |
| Internet Crime Complaint Center (IC3) | Online fraud and cybercrime |
| Your state attorney general | Local consumer protection issues |
| Social Security Administration | SSA impersonation specifically |
One important truth: scam reporting is undercounted because many victims feel embarrassed. If you’ve been targeted or lost money, reporting is not about shame. It’s about preventing the same thing from happening to someone else. These scams operate on volume. Every report helps law enforcement identify patterns.
“The moment someone tells you not to hang up, not to verify, and not to tell your family, that’s the moment you should do all three.”
You can follow a practical scam prevention guide to build stronger habits, and if you or someone you know has already been targeted, scam victim support resources can help with next steps and recovery.
Pro Tip: Save your bank’s official phone number directly in your contacts right now. The next time you get a suspicious text or call claiming to be from your bank, you’ll already have the real number to verify against.
The uncomfortable truth about impersonation scams: Why education still falls short
Here’s something most guides won’t tell you. Awareness campaigns, including this one, are not enough on their own.
Every year, billions of dollars are spent on cybersecurity education. Warning labels are added to emails. Banks send reminders. The FTC runs public campaigns. And yet the losses keep growing, and core psychological tactics have stayed exactly the same even as the technology behind them evolves. That tells us something important. Knowledge doesn’t automatically change behavior under stress.
When someone calls you and says your grandson has been arrested and needs bail money tonight, you don’t think. You feel. Fear, love, and panic kick in. At that moment, everything you’ve read about scams evaporates. This is not a personal failure. It’s human nature. Scammers have spent years studying how to trigger exactly that response.
The people who avoid falling victim aren’t necessarily better informed. They’re people who have built reflexive habits: always hang up and call back on an official number, always verify before paying, always slow down. These habits work because they don’t require you to think clearly in a high-stress moment. They’re automatic.
We’ve seen this pattern in our own research and in the cases we review. The victims of impersonation scams include doctors, lawyers, teachers, and IT professionals. Smart, careful people who were caught at a vulnerable moment. That should make all of us pay attention, not feel superior.
The other uncomfortable reality is that real phishing analysis shows how convincing modern scam communications have become. Spoofed bank logos, perfect grammar, and cloned websites that look identical to the real thing are now standard. Spotting a scam is no longer about looking for bad spelling or strange formatting. You need a systematic approach.
The most effective prevention strategy is this: remove urgency from your decision-making. If something must happen immediately, that’s the sign to slow down, not speed up. Real banks, government agencies, and service providers can wait five minutes while you independently verify who you’re talking to. Scammers cannot.
Building these habits now, before something happens, is the single most effective thing you can do. Share them with older family members. Practice them yourself. Make independent verification a non-negotiable reflex.
How ScamKit can help you stay protected
If you want to put this knowledge into practice, ScamKit’s interactive tools are designed to make scam detection second nature.
ScamKit is built for exactly the situations this article describes. When you receive a suspicious link in a text or email, you can check suspicious links instantly using ScamKit’s free URL Checker. No sign-up required. No personal information needed. Just paste the link and get an immediate risk assessment. For anyone who wants to practice identifying real scam tactics before encountering them, the interactive scam simulator walks you through realistic scam scenarios and helps you build the reflexes that actually protect you when it counts. ScamKit’s guides, phone number screening, and message analysis tools give you a complete toolkit to stay ahead of impersonation scams.
Frequently asked questions
What are warning signs of impersonation scams?
Urgency, threats, requests for secrecy, and demands for untraceable payments like gift cards, wire transfers, or cryptocurrency are the clearest warning signs that you’re dealing with a scam.
Who is most at risk for impersonation scams?
Older adults aged 60 and older face disproportionately high losses, though anyone unfamiliar with scam patterns, especially those targeted through tech support or government impersonation tactics, remains vulnerable.
What should I do if I think I received a scam call or message?
Pause, verify independently using official sources, and report the scam to the FTC or your bank. Independent verification is essential and never use contact information provided by the person who contacted you.
How do impersonation scams use technology to deceive?
Scammers use spoofing and AI tools including cloned voices and fake websites to create convincing impersonations of people and institutions you already trust.
Why are impersonation scams so effective?
They work because psychological tactics like authority and secrecy target your emotions rather than your logic, making them effective even against people who know scams exist and believe they would never fall for one.